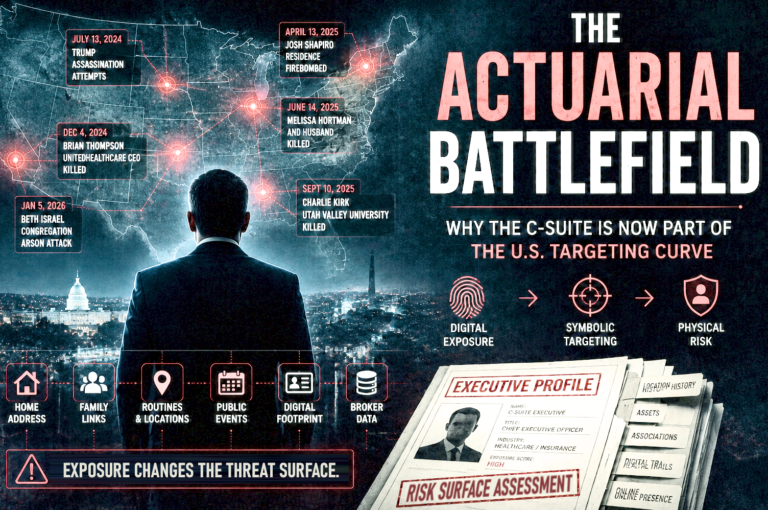
The Actuarial Battlefield
Why the C-Suite Is Now Part of the U.S. Targeting Curve The actuarial battlefield is the risk environment where public grievance, exposed personal data, symbolic targeting, and corporate governance collide. In this environment, executives are not only protected as individuals. They are priced, modeled, insured, monitored, and targeted as extensions of the institutions they represent….