How Consolidation Rewired the Risk Layer in 2026
Domain intelligence is no longer a security discipline.
It is a financial asset class.
Private equity owns registrars.
Payment networks own threat intelligence firms.
Holding companies control passive DNS and infrastructure telemetry.
The logos still look independent.
The backend ownership does not.
Recorded Future now sits inside Mastercard.
SecurityTrails sits beneath Recorded Future.
DNS Spy sits beneath SecurityTrails.
That is not brand diversity.
That is vertical control of signal.
If you are still attributing domains by registrar name, you are already wrong.
You are attributing storefronts. Not control planes.

“Brand is marketing. Infrastructure is truth.”
— Colby Scullion, OIQ
That has consequences for
- Signal normalization
- Attribution accuracy
- Analyst decision velocity
The Financialization of Domain Intelligence
Ownership concentration is not cosmetic. It changes incentives.
When intelligence platforms sit inside financial institutions, signals are normalized differently. Risk scoring integrates earlier. Domain telemetry becomes transaction context.
A defining feature of the current landscape is ownership concentration. Recent transactions make the trend impossible to ignore:
- Namecheap acquired by CVC Capital Partners for $1.5B
- MarkMonitor divested by Newfold Digital and sold to Com Laude, backed by PX3 Partners
- Recorded Future acquired by Mastercard for $2.65B
Not passive investments. They signal a reclassification of domain intelligence from “security tooling” to “enterprise risk asset.”
Mastercard’s move is especially instructive. Recorded Future now sits alongside fraud scoring, transaction monitoring, and financial crime intelligence. Domains are treated as financial risk indicators, not just technical artifacts.
Mastercard’s DNS acquisition stack runs at least four layers deep. Recorded Future owns SecurityTrails, and SecurityTrails acquired DNS Spy in 2020. This suggests that MasterCard is developing a very deep bench of capabilities to detect changes on the internet.
This alters incentives, integration paths, and signal normalization.
This consolidation does not just change ownership. It breaks attribution models.
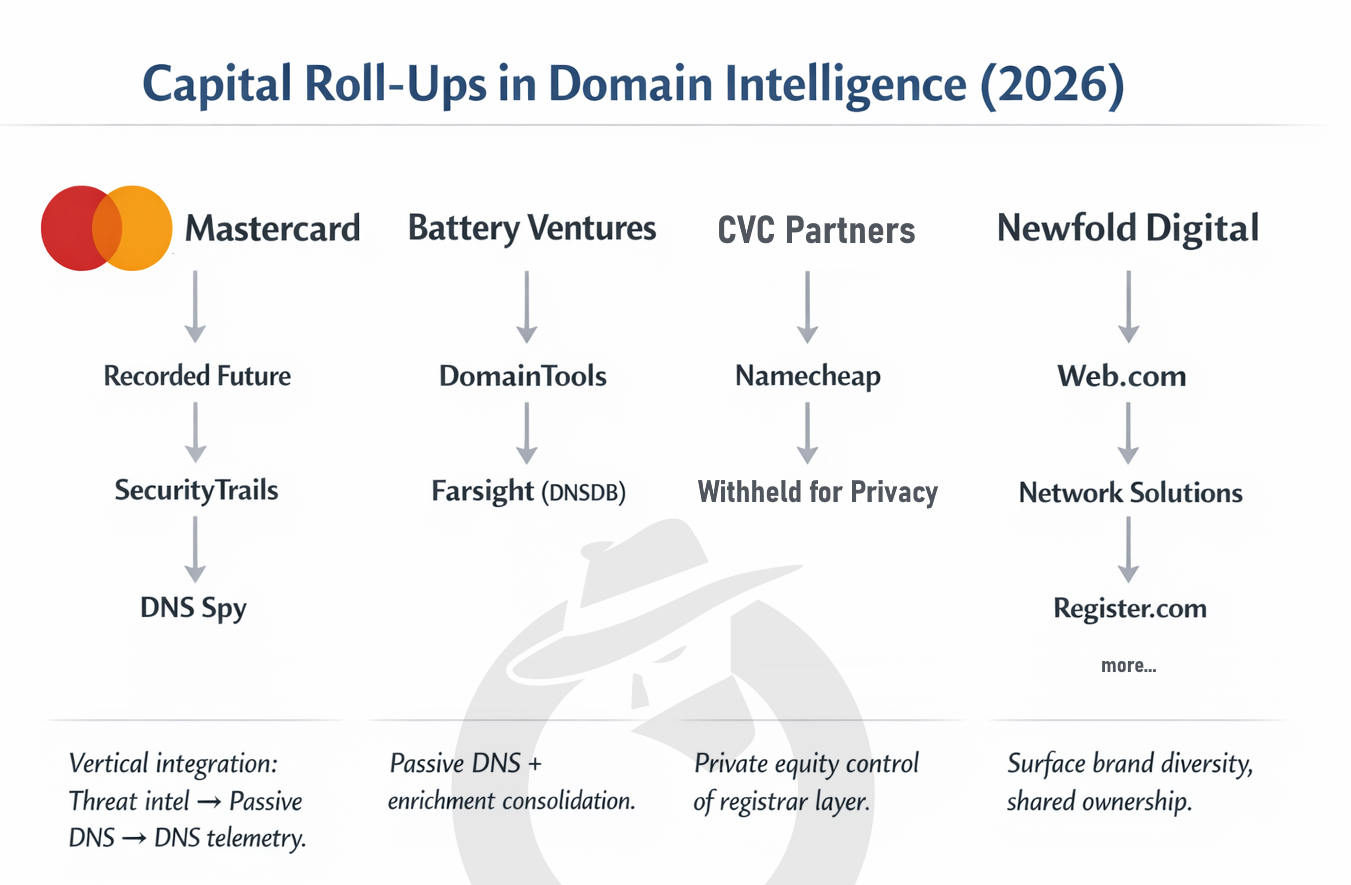
Capital Roll-Ups in Domain Intelligence (2026): Vertical integration across threat intel, passive DNS, and registrar layers
Even Financial Giants Leak at the DNS Layer
In 2024, researchers noted that Mastercard’s DNS records contained a subtle but serious typo. For years, certain records pointed to akam.ne instead of akam.net
One missing letter. Five years exposed.
The misconfiguration created redirect risk under the right conditions. Two takeaways:
Infrastructure errors persist longer than executives assume.
Owning intelligence capabilities does not eliminate operational fragility.
The paradox of consolidation:
The deeper the stack, the greater the surface area for small mistakes to create outsized risk. Small DNS artifacts become leverage points when adversaries monitor the same stack you do.
Why Brand-Based Attribution No Longer Works
Consolidation has a hidden cost. Data ambiguity.
As distinct brands are absorbed into holding companies, their operational identities blur. Legacy assumptions break.
Examples:
- Multiple registrars sharing backend infrastructure
- Separate brands using identical DNS providers
- Privacy services pooled across corporate siblings
This breaks:
Registrar-based clustering
Brand-based risk scoring
Single-axis enrichment workflows
Attribution based on registrar name alone is now unreliable. Analysts must dig deeper.
What matters now:
- Nameserver patterns
- Autonomous System Numbers
- Certificate Authorities
- Hosting and DNS reuse across brands
Control-plane infrastructure, not storefront labels
In short, domain intelligence has shifted from surface attribution to stack-level analysis.
When attribution models collapse, predictive models become the advantage.
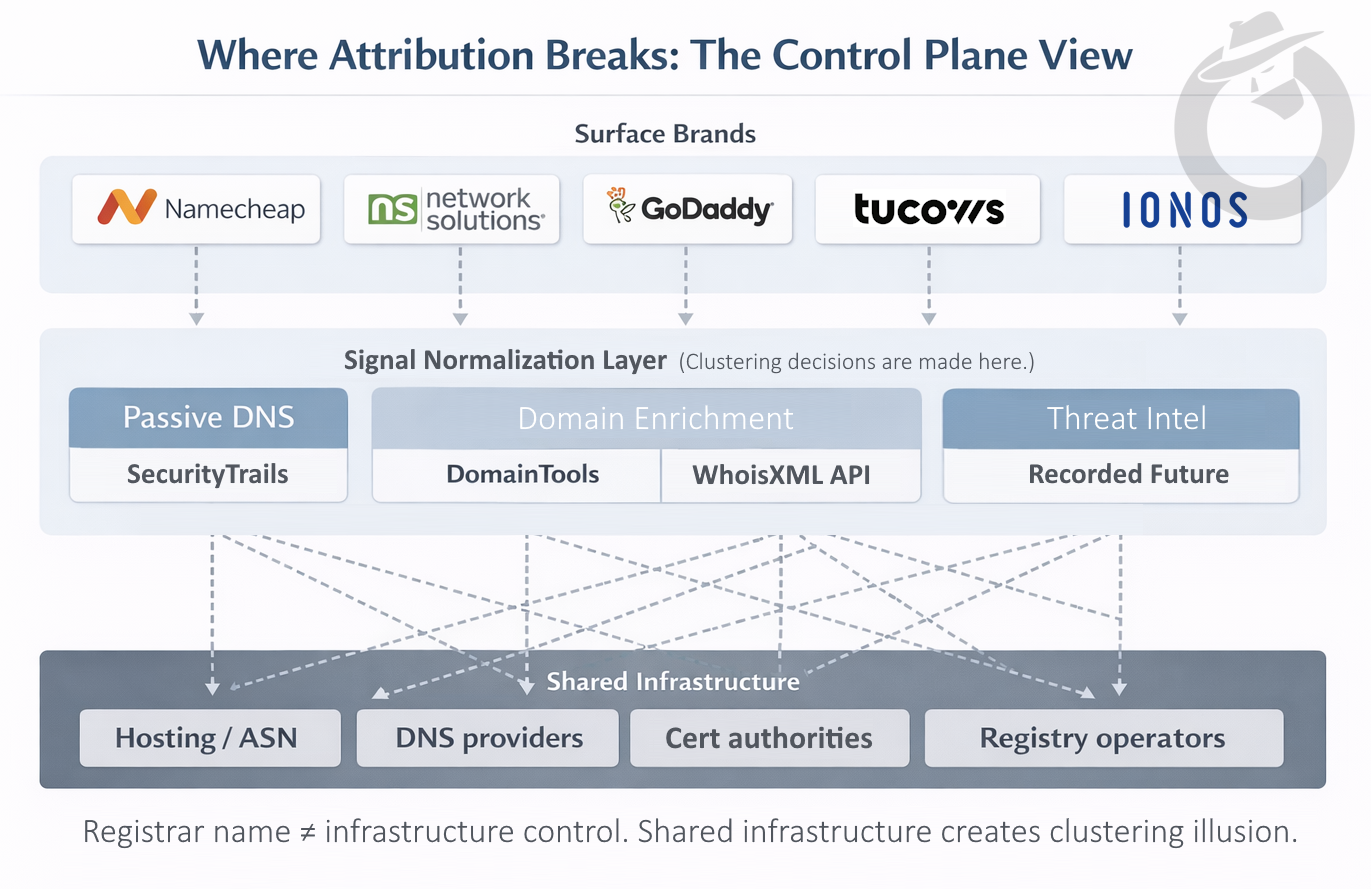
Where Attribution Breaks: Registrar name ≠ infrastructure control. Shared infrastructure creates clustering illusion.
What “Pre-Attack Visibility” Actually Means in 2026
When we say premium providers now compete on pre-attack visibility, we are not talking about faster alerts.
We are talking about time advantage.
Pre-attack, or “Left-of-Boom,” visibility means identifying malicious infrastructure before it is operationally used. Not after a phishing email lands. Not after malware detonates. Before the campaign exists in the wild.
This capability sits upstream of traditional SOC detection.
How Pre-Attack Intelligence Is Generated
Pre-attack visibility relies on signals that most legacy tools ignore or underweight.
Key indicators include:
- Domain registrations with adversary-specific linguistic patterns
- Early DNS resolution behavior inconsistent with benign use
- Hosting and ASN reuse tied to known operators
- Certificate issuance timing and anomalies
- Infrastructure staging behavior across related domains
Individually, these signals are weak.
Clustered correctly, they become predictive.
Prediction emerges from correlation across time, not single-event indicators.
Temporal stacking matters more than raw feed volume.
Why This Is Now the Premium Tier
The shift happened because defenders lost the speed race.
Attack infrastructure is cheap. Disposable. Automated.
Waiting for weaponization guarantees late detection.
High-maturity intelligence teams now prioritize:
- Early containment
- Campaign disruption before delivery
- Reduced incident response cost
- Fewer downstream alerts
Pre-attack intelligence does not replace SOC tooling.
It changes what the SOC never has to see.
Why Consolidation Accelerated This Shift
Consolidation made pre-attack intelligence viable at scale.
Mergers like HYAS into Silent Push collapse multiple datasets into a single analytical plane:
- Passive DNS
- Domain lifecycle data
- Adversary infrastructure history
- Pre-weaponization signals
This reduces friction.
It increases confidence.
It lowers false positives.
Standalone feeds cannot do this reliably.
The Operational Consequence
Organizations with pre-attack visibility operate in a different time horizon. They pivot from reactive IOC ingestion to infrastructure disruption.
They:
- Block infrastructure before it delivers payloads
- Attribute campaigns earlier
- Shift analysts from triage to disruption
- Measure success by non-events, not incidents
This is why predictive clustering at scale defines the premium tier.
Not because it is impressive.
Because it quietly prevents problems that never appear on a dashboard.
“Left-of-Boom” Intelligence Is Now Table Stakes
Quiet prevention is the measurable outcome.
This is no longer optional.
The acquisition of HYAS by Silent Push in late 2025 formalized a broader trend. Distinct intelligence disciplines are merging:
- Adversary C2 infrastructure tracking
- Pre-weaponized domain detection
- DNS-based early warning
- Infrastructure pivot analysis
The result is unified adversary infrastructure intelligence.
Detection happens before payloads.
Before phishing.
Before malware delivery.
This is what buyers now expect at the high end.
Anything less is commodity OSINT.
The Reality of the 2026 Domain Ecosystem
Our review evaluated over 100 entities across the domain intelligence landscape.
What we found:
- Extreme concentration under a small number of parent organizations
- Multiple layers of indirect ownership
- Widespread reuse of technical infrastructure across “competing” brands
- Inconsistent or outdated tagging in most public datasets
This creates real operational risk.
Misclassification leads to:
- Faulty attribution
- Broken threat clustering
- Overconfident conclusions based on brand labels
Analysts who rely on single-axis categorization are flying blind.
Why Taxonomy Now Matters More Than Ever
More feeds will not fix this. Structure will.
If your taxonomy cannot map ownership, infrastructure dependency, and temporal signal class, your clustering will drift.
We recommend a multi-axial taxonomy that reflects operational reality, not marketing categories.
At minimum, classification should capture:
- Corporate ownership and financial control
- Technical infrastructure dependencies
- Functional role in the domain lifecycle
- Intelligence use case alignment
- Visibility depth and temporal value
This allows analysts to answer modern questions:
- Who controls the authoritative infrastructure behind this domain?
- What other infrastructure moves with it?
- Is this signal pre-attack or post-compromise?
- Is this data suited for attribution or only enrichment?
Static labels cannot answer dynamic risk questions.
Domain Intelligence Is Now Power Infrastructure
The domain ecosystem has crossed a threshold.
It is no longer just part of cybersecurity.
It is part of global financial risk management.
That reality demands higher standards.
Better attribution methods.
Deeper technical analysis.
Taxonomies built for how domains are actually used, traded, and exploited.
In 2026, domain intelligence is not about who sells the data.
It is about who controls the stack.
And whether your analytic models account for that control.