Featured Content from ObscureIQ
Digital Footprint
Domain History Is Forever
January 23, 2026
Domain History Is Forever. Plan Accordingly. Registering a domain is a disclosure event. It is not a private act. You…
attack surface mappingattribution riskdata aggregationdigital footprintdomain correlation
Analysis
The Top 10 Threats to Executives in 2025
December 10, 2025
The Top 10 Threats to Executives in 2025: From Boardrooms to Backyards The risks executives face are no longer confined…
assassination risksfamily exploitationhome invasioninsider threatskidnapping threats
Anonymous Payments
The Strategic Guide to Virtual Credit Cards
November 14, 2025
Why VCCs Don’t Grant Anonymity. And How to Use Them for Maximum Compartmentalization and Breach Protection Virtual credit cards (VCCs)…
apple paycapital one enociti vanscompartmentalized paymentsfinancial data protection
Analysis
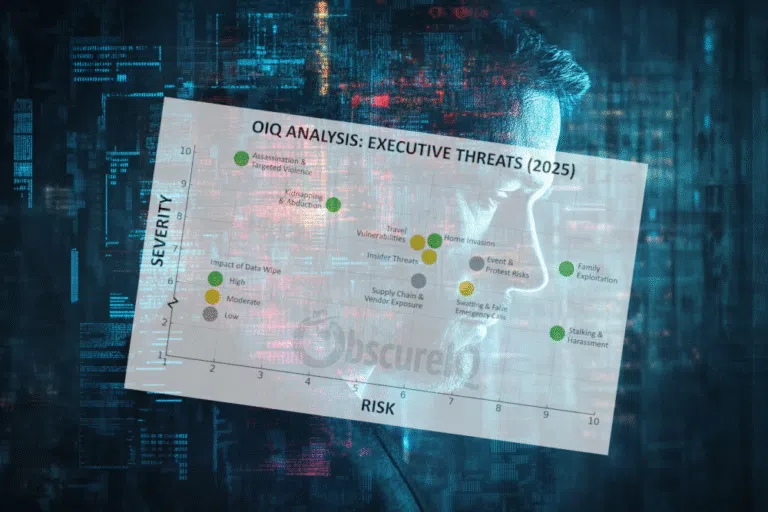
The Executive Threat Matrix: How Data Wipes Shift the Risk
October 17, 2025
The Executive Threat Matrix: How Data Wipes Shift the Risk Executives face ten major categories of threat in 2025. Each…
data-suppressiondata-wipesdigital footprintfamily exploitationfootprint erasure
Analysis
Why Deepfakes Are Harder to Stop Than We Admit
September 4, 2025
I mapped dozens of proposed solutions to deepfakes. The result was sobering:No silver bullets. Only tradeoffs. The conversation around deepfakes…
deepfake detectorgovernment regulationprovenance toolsrapid takedownstech ban
Credible Threats
Signals in Plain Sight (Covert Communication Channels)
July 4, 2025
At ObscureIQ, we’re rolling out ThreatWatch. It’s our new active threat monitoring service. Looking for threats forces us to think…
emoji substitutionshidden messagesin-game chatmod-based signalingsteganography
Analysis
Brokers & Doxxers: From Exposure to Exploitation
June 11, 2025
Brokers & Doxxers: From Exposure to Exploitation Every week we hear from clients who discover their address, phone number, or…
anti-doxxingcybercrimeexploitationexposureharrassment