Narrative Warfare:
What If JFK Was Killed in 2026?
Adversaries Exploit the Moment. Deepfakes, Martyrs, and the Collapse of Trust in Real Time.
Dallas. Motorcade. Noon light. Phones already up.
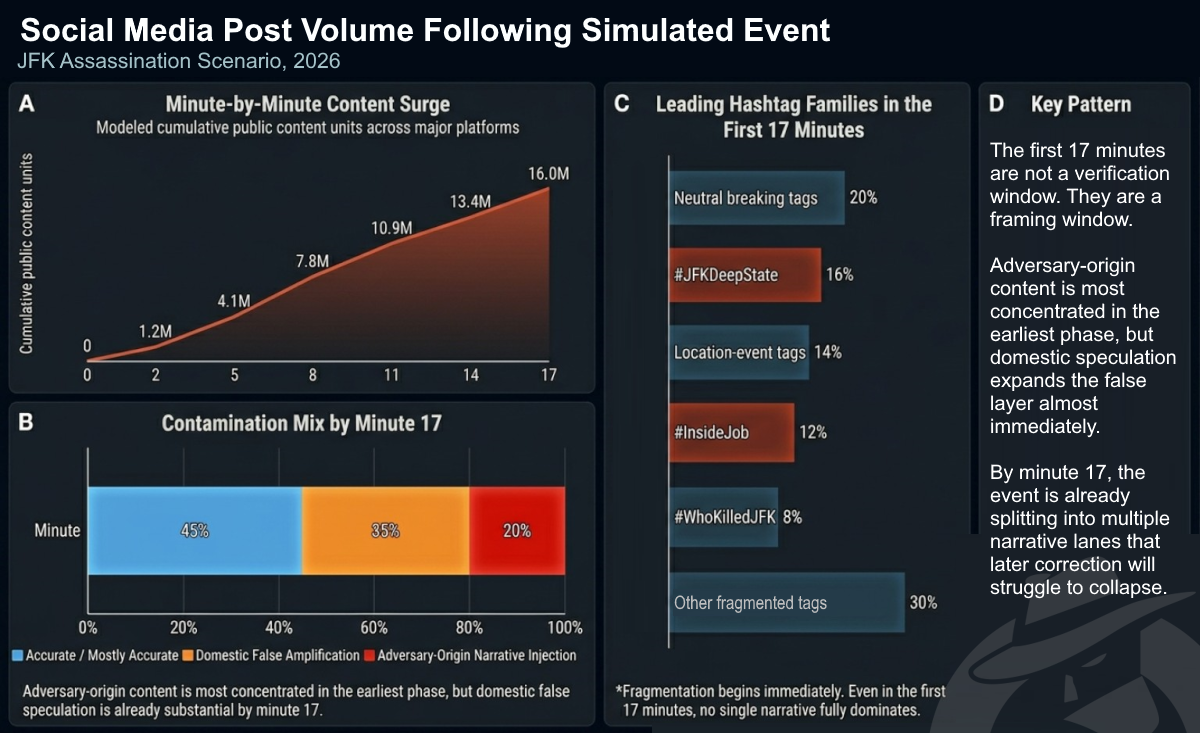
The first shot lands before anyone understands what they are seeing. The second clip appears before the first official statement. By the time the motorcade stops, the event is already splintering across X, TikTok, YouTube, Telegram, Reddit. One angle shows the hit. Another claims the agents stepped aside. A slowed-down clip begins circulating with red circles and arrows. Someone names a suspect. Someone names the wrong suspect. Someone posts that the real story is the stand-down. Someone else says the shooter was about to expose everything.
No grainy Zapruder film. No long vacuum before the public sees the evidence. This time it is 4K, multi-angle, real-time, algorithmically accelerated. The first millions do not wait for confirmation. They watch, react, repost, speculate, accuse. Synthetic audio drops. A witness account appears that never existed. A hashtag hardens. A false frame picks up domestic voices. Within minutes, the question is no longer just what happened. The question is what kind of story people now believe they are living inside.
The death is the trigger.
The narrative war is the event.
This paper is not about whether a president could be killed on camera in 2026. It is about what happens to a country when belief forms faster than verification, when adversaries arrive with pre-built narratives, when domestic influencers scale those narratives before institutions can establish basic facts, and when the damage does not stop at social media but spills into markets, logistics, public order, and trust itself.
In that environment, the first battle is not over evidence. It is over narrative structure. Lose that, and everything that follows — from suspect identification to national response to economic stability — unfolds inside a contaminated frame.
This paper uses a 2026 JFK-style assassination scenario as a pressure test. Not a prediction. Every tactic described has a documented precedent in operations conducted between 2013 and 2024. The goal is to make abstract adversary playbooks concrete and actionable for practitioners in OSINT, counter-narrative operations, crisis communications, and executive protection.
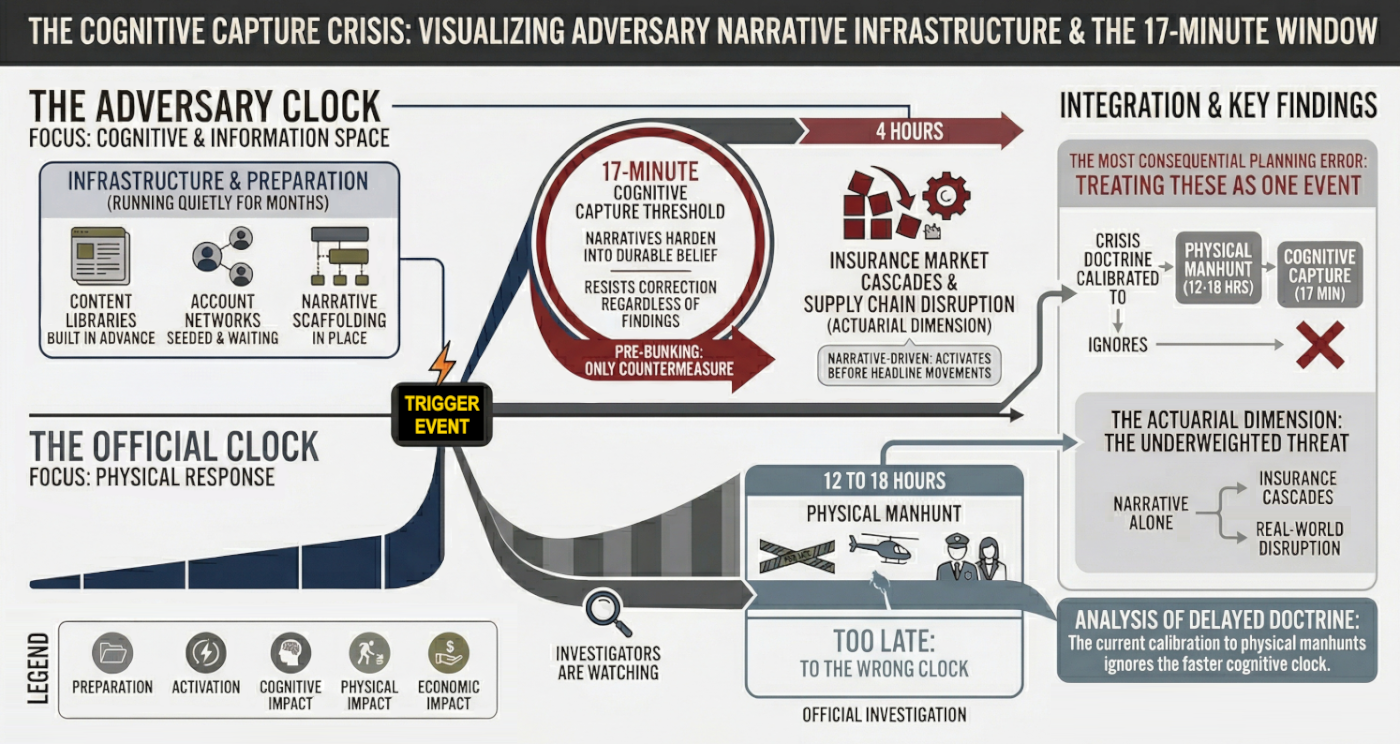
The event starts two clocks.
The first is the official clock. It tracks the physical crisis. Shots fired. Scene secured. Suspect identified. Manhunt launched. Evidence collected. Briefings prepared. This is the clock institutions understand. It runs for hours, sometimes days.
The second is the adversary clock. It tracks belief formation. First clip. First caption. First accusation. First false witness. First emotional frame that feels clear enough to repeat. This clock moves in minutes. It does not wait for forensic certainty. It does not need complete facts. It only needs enough ambiguity to turn shock into a story people can use.
Those clocks do not run at the same speed, and they do not decide the same outcome. The official clock may determine who pulled the trigger. The adversary clock determines what millions of people think the event means before the investigation has even begun. That is the central problem this paper explores. The manhunt may last 12 to 18 hours. Cognitive capture begins far earlier. Treating those timelines as one is the most consequential planning error in modern crisis response.
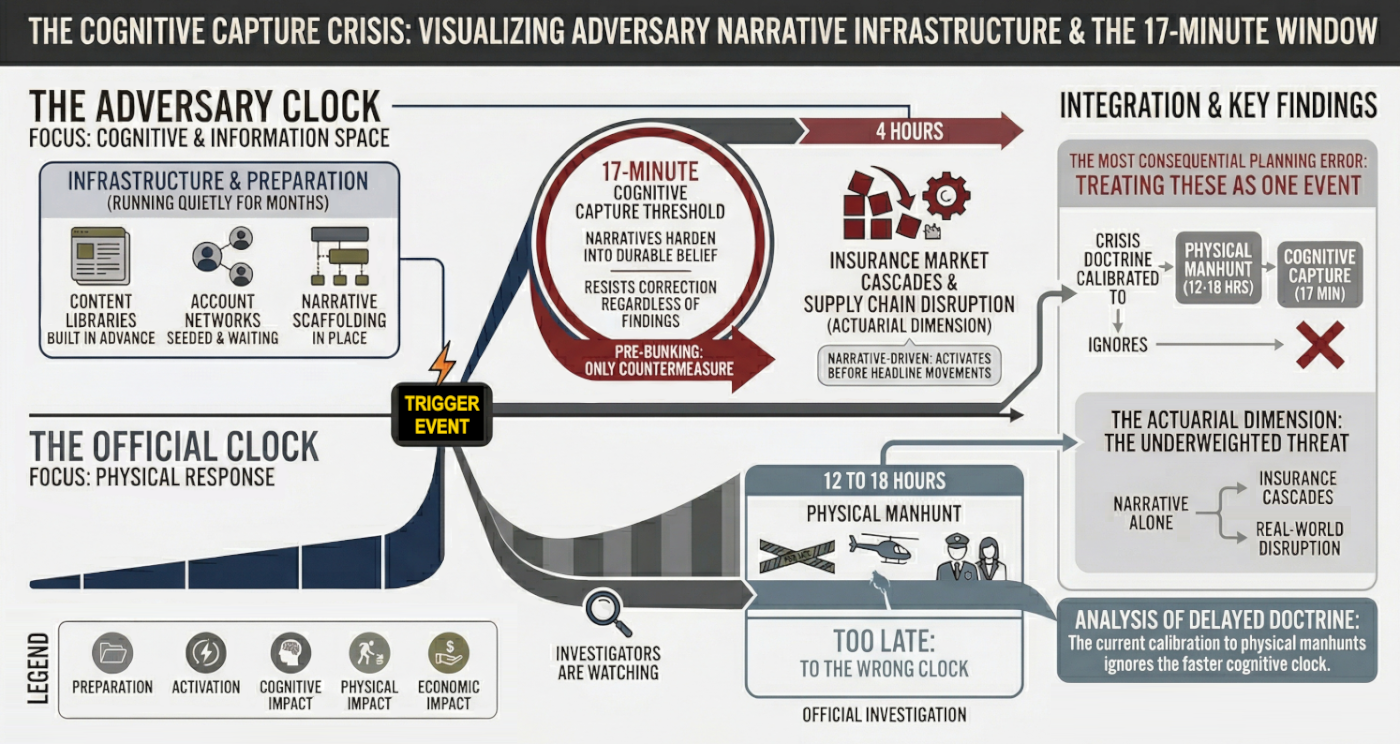
There are two distinct timelines running in parallel from the moment of the first shot. The first is the physical manhunt. The second is cognitive capture, the process by which audiences form beliefs that will not meaningfully update regardless of what official investigations find. These two timelines operate on radically different clocks.
The first 17 minutes are not important because they produce certainty. They matter because they produce structure.
In a high-salience crisis, audiences do not wait for full verification. They reach for the first explanation that feels legible, emotionally usable, and socially repeatable. That initial frame is often established before institutions can verify basic facts, and once it is adopted by high-reach accounts, later correction loses leverage. This is why the "17-minute threshold" should be treated as a planning threshold, not a literal constant. Its value is operational. If your response posture begins at 30 minutes, you are already operating inside an occupied information environment.
The core mistake in most crisis doctrine is treating the physical event and the narrative event as the same timeline. They are not. The manhunt may last 12 to 18 hours. Cognitive capture begins much earlier. In practice, the decisive question is not when investigators solve the event. It is when the public decides what kind of story it is hearing.
What the 17-Minute Threshold Actually Means
The threshold is best understood as a short sequence rather than a stopwatch.
The claim is not that every mind is made up by minute 17. The claim is that the initial structure of belief may become sticky enough within that period that every later response starts from a position of disadvantage. In fast crisis environments, the first trusted frame often matters more than the first verified fact.
| Phase | Duration | Primary Mechanism | Effective Countermeasure |
|---|---|---|---|
| Imprint | 0 to 17 Minutes | Affect-driven processing; first-frame adoption before verification is possible | Pre-bunking; pre-approved holding statements deployable in under 5 minutes |
| Adoption | 17 Min to 4 Hours | Reinforcement via newsbrokers; socialized belief spreading through high-reach amplifiers | Platform coordination; high-reach correction through pre-established trust and safety channels |
| Resistance | 4 Hours to Day 3 | Narrative encampment; cognitive dissonance filtering out corrective information | Delegated authority communications; long-tail counter-narrative work |
The practical implication is straightforward. If an institution waits for full verification before establishing any interpretive frame at all, it is likely to enter the fight after cognitive capture has already begun. That is why pre-bunking, pre-approved holding statements, and pre-event narrative mapping are not enhancements. They are the only measures that operate on the same clock as the problem.
Why Audiences Adopt Contaminated Narratives
People do not adopt contaminated narratives only because they are false. They adopt them because those narratives outperform verified information on three dimensions that matter in crisis: veracity, emotional appeal, and relevance.
Research on crisis information consumption points to a model known as VER: Veracity, Emotional Appeal, and Relevance. In normal conditions, veracity carries more weight. In a high-uncertainty event, emotional appeal and perceived relevance surge. Fear, anger, disgust, identity threat, and moral outrage create demand for narratives that feel clarifying, even when they are wrong. That is why contaminated narratives often spread not in spite of their flaws, but because they are better fitted to the emotional needs of the moment.
This helps explain why falsehood can dominate the environment even when verified facts exist. False claims are often more novel, more emotionally charged, and more identity-confirming than the truth. They travel faster, resolve more slowly, and remain socially useful long after they have been debunked. The result is not just misinformation. It is narrative contamination, where false or unverified frames become the public's working reality before institutions can establish an authoritative account.
The Decline of Legacy Corroboration and the Rise of the Newsbroker
The modern crisis information environment is no longer organized around institutional confirmation. It is organized around speed, reach, and narrative brokerage.
In earlier media systems, legacy outlets played a larger corroboration role. They did not eliminate rumor, but they imposed delay, editorial friction, and a stronger norm of confirmation before amplification. That function has weakened. In the current environment, a small class of high-engagement influencer accounts, pseudonymous aggregators, and partisan interpreters increasingly acts as the first layer of narrative authority. These actors, often called newsbrokers, dominate crisis discourse by rapidly packaging speculation, clips, screenshots, and interpretive claims into shareable frames before traditional institutions can respond.
This is a structural shift, not a platform quirk. During fast-moving crises, the question is no longer simply whether official sources are trusted. It is whether they can even enter the conversation early enough to matter. Newsbrokers thrive inside that gap. They do not need to prove a theory. They need to name the moment first, give it emotional direction, and supply a frame that others can repeat. Once that happens, institutional statements are demoted from primary sensemaking tools to one input among many.
Legacy corroboration declines not only because trust has eroded, but because timing has collapsed. By the time a cautious institution confirms what happened, the public may already have accepted a brokered explanation that is more emotionally satisfying, more identity-aligned, and more socially portable. In that environment, the first narrative broker often matters more than the first verified source.
Observable Markers of Cognitive Capture
- A stable accusation frame emerges before official verification
- The same core narrative appears across multiple platforms with audience-specific captioning
- High-reach domestic accounts begin repeating the frame without adversary attribution
- Misidentification converges around a named individual or small suspect pool
- Corrective content spreads more slowly than the original framing
- Users begin treating fabricated or unverified artifacts as already established fact

Precedent Evidence Base
Assumption vs. 2026 Reality
| Segment | Prior Assumption | 2026 Reality |
|---|---|---|
| Narrative saturation | Hour 0–2 | Min 0–17 |
| Suspect ID | 0–4 hours | Instantaneous (OSINT) |
| Martyr launch | Hour 6–12 | Min 30–Hour 2 |
| Economic reaction | Day 3 | Hour 1–4 |
The first wave is not shaped by one actor alone. It begins with foreign adversaries because they arrive prepared, with pre-built content, frames, and timing. But it hardens only when domestic actors give those frames legitimacy, speed, and cultural fluency. In a modern crisis, the real question is not only who injects the first narrative. It is who makes that narrative socially usable.
They flood the zone with "evidence" that it's an inside job. Deepfakes of Secret Service agents turning away, leaked memos from "whistleblowers" (all fabricated, all traceable to state actors). Their angle: "America's elite are eating their own." Goal: Make the U.S. look weak, divided, ungovernable.
They push a cross-spectrum bridge narrative designed to activate both ends of the political spectrum simultaneously. The same payload, different captions: one version routes through anti-imperialist distrust of intelligence agencies, the other through conspiratorial distrust of globalist elites. Both groups receive identical raw clips. The framing does the targeting.
They also leak "classified" audio: a politically salient synthetic clip framed as a leaked recording from a prior administration, joking about "taking out threats." Fake, but emotionally true enough. People don't fact-check when they're mad. Research on affect-driven processing consistently shows that high emotional arousal degrades verification behavior. The content doesn't need to be convincing. It needs to arrive first.
The Synthetic Witness Layer: Novel Capability
Beyond deepfakes and fabricated documents, China deploys a third content category that is harder to detect and faster to believe: AI-generated bystander accounts providing cross-platform eyewitness testimony. These are fully constructed personas with profile histories, location metadata, and posting patterns.
Hour 0 to 6: Flood the Zone
State-linked accounts on Weibo and Douyin drop the first wave: ultra-realistic deepfakes. Secret Service agents visibly stepping aside in slowed-down drone footage (AI-generated, 60fps, perfect lip-sync). A "whistleblower memo" from a supposed NSA contractor appears on Telegram and is reposted to Reddit within minutes, watermarked with authentic-looking classification stamps.
Left-leaning audiences get the "military-industrial complex finally cashed in its chips" version. Right-leaning audiences get the "deep-state coup" version. Both groups receive the exact same raw clips. The only difference is the caption.
Hour 6 to 48: Cross-Spectrum Goes Viral
Chinese state media publishes the first "investigative" pieces in English, framing the hit as a coordinated intelligence operation. Tens of thousands of freshly spun accounts then flood Western platforms. By hour 36, #JFKDeepState is trending globally. American users do most of the amplification work. China supplies the original payload.
This is what the first wave looks like in practice. The stand-down deepfake performs an imprint function — it converts uncertainty into apparent visual accusation before any institution can establish basic facts.
#JFKDeepState #InsideJob

What it targets: Secret Service legitimacy, institutional trust, accountability narratives.
What it unlocks next: Cable pickup, elite complicity framing, slower correction cycle.
More chaotic, more personal. They weaponize the suspect. Call him lone wolf, ex-Marine, QAnon-adjacent. Russia doesn't invent him; they just amplify him. RT runs a 24-hour special: "The Patriot Who Saw Too Much."
They dox his family, release edited videos of him ranting about "the deep state," then pivot: "See? He was right." Goal: Turn the killer into a martyr. Simultaneously, they push a "false flag" counter-narrative. The shooter was a Ukrainian asset, or a Chinese plant. Muddy the water. Make every theory equally plausible.
Hour 0 to 6: Weaponize Before the Body Is Cold
RT and Sputnik flip to wall-to-wall coverage. Within ninety minutes #PatriotWhoSawTooMuch is trending. The narrative is locked: lone wolf? Yes. But a lone wolf who was right.
Hour 6 to 48: The Martyr Pivot
Family doxxing drops first. Then come the AI-edited garage rants. By hour 36 the story flips from "crazy gunman" to "tragic hero silenced by the machine." The emotional payload is pure venom.
Day 2 to 3: False-Flag Cross-Pollination
Two parallel tracks launch: "Ukrainian asset" theory and "Chinese plant" theory. Neither needs to win. The point is to make the official "lone wolf" narrative look laughably incomplete.
Endgame for Russia
They don't want America to pick a single villain. They want Americans to pick all of them at once. By day seven the country is fractured into hostile camps: one side canonizing Oswald as the new John Brown, another screaming "Russian psyop," and everyone convinced the institutions are lying.
Foreign actors do not need to dominate the first wave for long. They only need to seed frames that domestic actors can carry in native language. Once newsbrokers, influencers, crowd analysts, and partisan interpreters begin repeating the payload without foreign fingerprints, the frame stops looking foreign and starts looking like common sense. That is when seeding becomes shaping. The first wave is not won when the adversary posts. It is won when domestic actors make the post socially portable.
| Time | Actor | Action | Effect |
|---|---|---|---|
| Hr 0–2 | Both | First 4K clips viral. China drops deepfake. Russia #PatriotWhoSawTooMuch. | ID speculation before FBI speaks. |
| Hr 2–6 | China | "Leaked NSA memo" Telegram to Reddit. Stand-down deepfake. | Official counter-narrative losing the race. |
| Hr 6–12 | Russia | Doxxing wave. AI-edited rant. RT 24-hr special begins. | Martyr frame locked in. |
| Day 1 | Both | FBI names suspect. Synthetic audio deepfake. First protests form. | Official story = one theory among many. |
| Late D1 | Russia | Suspect cornered/killed. "He was about to reveal everything" package drops. | Capture accelerates fracture. |
| Day 2 | Both | #OswaldWasRight 2.4M posts. TikTok stitch 47M views. | Cross-pollination peaks. |
| Day 3 | Both | False-flag tracks launch. Armed rallies. Stock futures down 4%. | Physical world reflects info environment. |
| Day 4–5 | Domestic | Cable splits. Martyr merch appears. | Institutional trust drops sharply (projection). |
| Day 6–7 | Both | National funeral. Markets down significantly (illustrative). | Fracture persistent. No unified narrative (projection). |
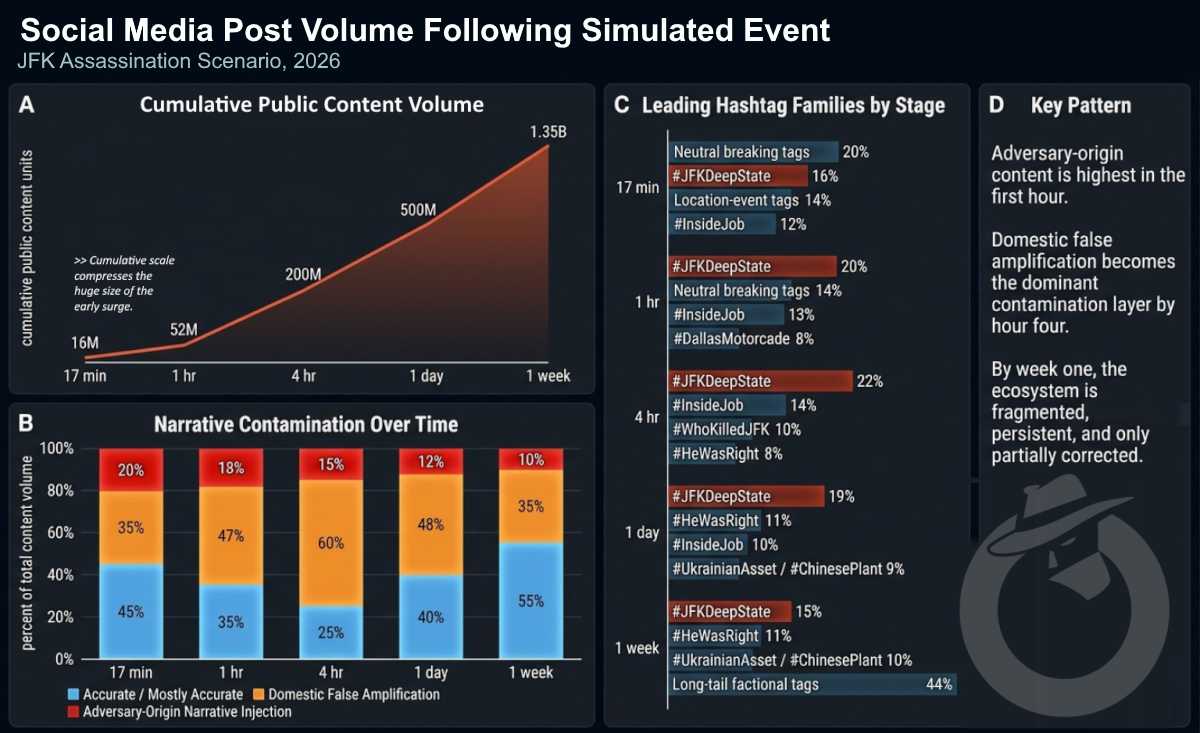
By Day 3, the spread mechanism has shifted from adversary injection to domestic amplification. The false-flag crossover thread shows how incompatible attributions combine to make the official narrative look incomplete even when it is accurate.
1. Bank records → Chinese crypto wallet.
2. Edited meetup photo in Poland with "SBU handler."
They played him from BOTH sides. Lone wolf? No. Patsy.
#JFKDeepState #PatriotWhoSawTooMuch
What it targets: Attribution confidence and investigative legitimacy.
What it unlocks next: Durable "official story is incomplete" framing.
The stock market declining by Day 7 is an outcome. The mechanism begins within the first few hours, operating through a channel most narrative warfare analysis ignores entirely: the insurance and financial risk infrastructure that underlies the physical economy.
The February 2026 Strait of Hormuz crisis provided the clearest modern precedent. The strait was not closed through military force. It was closed through insurance. Protection & Indemnity clubs issued 72-hour war risk cancellation notices. Additional War Risk Premiums spiked from 0.15% to over 1%. Major carriers rerouted within days, not because the military situation demanded it, but because the actuarial calculus made transit economically indefensible. B2
How Narrative Shock Becomes Economic Damage
The economic effects described in this analysis do not begin when markets fully price the event. They begin earlier, at the point where uncertainty enters the systems that underwrite movement, coverage, and automated decision-making. This is best understood not as a market story first, but as a risk transmission story.
In a high-salience crisis, the first meaningful reactions are often not visible in headline indices. They appear in the quieter infrastructure of risk: insurance language, routing assumptions, volatility clustering, internal advisories, and machine-driven de-risking behavior. These systems do not wait for public certainty. They react to perceived instability under conditions of incomplete information.
Cyber-to-Actuarial Transmission Path
This is why the first four hours matter. The claim is not that every information shock produces a full actuarial cascade. The claim is that in a sufficiently chaotic high-salience event, the earliest meaningful economic reactions may begin inside the first one to four hours, well before political facts are settled and well before public messaging catches up.
What to Monitor in the First Four Hours
- Changes in advisory language from insurers, maritime risk monitors, or freight security providers
- Abrupt tightening in political-risk phrasing tied to domestic instability
- Unusual volatility clustering around politically sensitive instruments
- Rapid circulation of fabricated financial screenshots or false institutional alerts
- Internal chatter among analysts or operators around "uncertainty premium" assumptions
- Divergence between physical conditions on the ground and the risk language used to price them
How the Media Splits
Legacy broadcast (ABC, CBS, NBC): Deliberate and cautious. The restraint reads, to audiences primed for distrust, as concealment.
Cable news, center-left: Focuses on security failures. Adversary content finds ready amplification by feeding the accountability narrative with fabricated evidence of deliberate stand-downs.
Cable news, right: Fragments fast. The martyr narrative finds its first mainstream foothold. By Day 2, the framing has calcified.
Independent / podcast ecosystem: Moves fastest, with least friction. Corrections, when they come, reach a fraction of the original audience.
International press: Covers the fracture as the story. Not the assassination. The American response to it.
How Politicians React
The Institutionalist (fictional archetype): Issues a measured statement within two hours. It generates roughly 12,000 engagements on a platform where the deepfake stand-down clip has 9 million views. Restraint gets reframed by adversary-adjacent accounts as cowardice or complicity.
The Opportunist (fictional archetype): Goes live within 90 minutes. Repeats an unverified detail from the Russia-seeded narrative. Walks it back six hours later. The walkback gets 3% of the original clip's reach.
The Conspiracist (fictional archetype): Posts within 45 minutes. Full martyr framing. Amplified by Russian bot networks within the hour, not because they coordinated directly, but because the content performs exactly the function they need.
It's the narrative environment that follows.

- Every group gets its version
- No one needs proof
- Emotional alignment replaces evidence
Truth becomes optional. Proof becomes secondary. Alignment becomes enough. And the next election? Whoever owns the narrative owns the country.
By Day 6, the adversary has largely withdrawn. The domestic ecosystem is self-sustaining. This post carries no adversary fingerprints — and it does not need them. The narrative has already been naturalized.
#NeverForget #JFKDeepState #OswaldWasRight
[Case-file collage: funeral procession still + all prior "evidence" items assembled with red thread. "Connect the dots." Fully domestic origin.]
What it targets: Public memory, grief, symbolic closure.
What it unlocks next: Long-tail repetition without foreign fingerprints.
If official resolution does not restore control, then the answer cannot be a better press conference after the fact. It has to be a faster operating model before the fact. That makes the next question operational: what can anyone with responsibility actually do inside the first hour, while the narrative is still forming?
The scenario above describes what adversaries do. This section describes what defenders should do in parallel. The first 60 minutes is not the time for comprehensive strategy. It is the time for pre-planned action. Every item below should be decided before an event, not during it.

What Has to Exist Before the Shot Is Fired
- Holding statements drafted and approved for high-probability crisis types
- Staff communications policy in place and understood by all personnel
- Dedicated synthetic media triage capacity assigned and trained
- Misidentification monitoring protocols and escalation paths established
- Platform trust and safety contacts identified and relationships active
- Actuarial monitoring triggers defined and assigned
- Economic coordination contacts identified and pre-briefed
1. Speed is structural, not tactical.
Adversary operations are not improvised in response to events. The content library, account networks, and narrative scaffolding are pre-positioned. The event is a trigger, not a starting point. Any response doctrine that treats Hour 0 as the beginning is already behind. Cognitive capture occurs at Minute 17.
2. OSINT is dual-use by definition.
The same crowd-sourced identification tools that can rapidly narrow a suspect field can converge on the wrong person just as fast. Misidentification at scale is not a risk. It is a near-certainty somewhere in the information ecosystem. The synthetic witness layer amplifies this further, as AI bystander accounts provide false confirmation that accelerates crowd convergence on incorrect identifications.
3. Proximity creates data exposure.
Every device in the blast radius of a high-profile event becomes part of the data environment. Bystanders are not passive witnesses. They are data sources being actively processed by multiple parties simultaneously, within minutes of the event. This applies to the economic layer as well, because device and location signals from financial district personnel feed algorithmic sentiment systems that trigger automated de-risking before any human decision is made.
4. Capture accelerates fracture.
Physical apprehension of a suspect does not close the information operation. In documented cases including Crocus, Bucha, and Butler 2024, the narrative war intensified after official resolution. The martyr package is pre-built. It deploys on death or capture.
The clock that matters is not the one investigators are watching. The central finding of this analysis is the 17-minute cognitive capture threshold: within approximately 17 minutes of a high-salience event, adversary narratives harden into durable belief that resists correction regardless of what official investigations subsequently establish. The physical manhunt runs for 12 to 18 hours. These two timelines are not the same event. Treating them as one is the most consequential planning error in current crisis response doctrine.
The actuarial dimension of this threat is the most underweighted. Narrative alone, without any physical action, is sufficient to trigger insurance market cascades that produce real-world supply chain disruption. The mechanism activates within 4 hours of a trigger event, well before any headline market move registers. Pre-bunking is the only countermeasure that operates inside the 17-minute window. Every doctrine calibrated to the physical manhunt clock rather than the cognitive capture clock arrives too late by design.
This white paper uses a 2026 JFK-style assassination scenario as a pressure test. Not a prediction. Every tactic described has a documented precedent in operations conducted between 2013 and 2024. The goal is to make abstract adversary playbooks concrete and actionable for practitioners in OSINT, counter-narrative operations, crisis communications, and executive protection.
- Deepfake video (60fps, 4K)
- AI-generated audio attribution
- Fabricated document injection
- Synthetic witness persona networks
- Weibo → Reddit → X bot seeding
- Cross-spectrum bridge narrative
- Martyr pivot package (pre-built)
- False-flag dual track (UA + CN)
- Zone-flooding: no single theory wins
- Domestic hand-off by Day 3
- P&I club war risk reassessment
- Freight route disruption
- Algorithmic sentiment de-risking
- Fabricated Bloomberg screenshots
- Supply chain disruption
- International attribution manipulation
- Evidence contamination
- Delegitimization of process
- Regulatory narrative exploitation
- 17-min capture threshold targeting
- OODA loop disruption
- Institutional trust collapse
- Affect-driven verification bypass
- Identity-targeted emotional payload
Quick Reference :: Instrument-to-Precedent Map
| Grey Zone Instrument | Primary Actor | Documented Precedent | Operational Effect |
|---|---|---|---|
| Synthetic Witnesses | China | Dragonbridge / Spamouflage (ongoing) | False eyewitness corroboration that forces audiences to evaluate people rather than media |
| Martyr Pivot | Russia | Prigozhin Mutiny, 2023 | Reframes perpetrator as whistleblower or tragic hero; suspicion of official investigation |
| Bridge Narratives | China / Russia | IRA 2016 Election Operations | Same raw content, divergent captions; cross-spectrum social fracture regardless of audience |
| False-Flag Tracks | Russia | Crocus City Hall, March 2024 | Parallel incompatible attributions produce interpretive exhaustion and delegitimize official findings |
This is a structured scenario exercise grounded in documented precedent, with illustrative operational assumptions where direct analogues do not exist. Every core tactic described has a real-world precedent in foreign influence operations conducted between 2014 and 2024. Where specific timing, volume, or outcome figures appear, they are scenario assumptions calibrated to be plausible, not empirical claims.
Scenario assumptions: Plausible illustrative projections (timing, volumes, sequencing) where no direct precedent exists.
Speculative escalations: High-confidence extensions of documented patterns into novel conditions, labeled where relevant. Readers should evaluate each layer on its own terms.
Precedents This Analysis Draws On
How to Read the Simulated Posts
The simulated posts in this analysis are not included merely to illustrate tone, platform aesthetics, or likely content formats. Each one represents a distinct operational function inside a broader narrative attack cycle. Their value is not just that they look plausible. Their value is that they show how different content types perform different jobs at different moments.

The first-wave deepfake post performs an imprint function. It converts uncertainty into apparent visual proof. The key feature is not sophistication alone. It is immediacy. A post framed as direct evidence of deliberate stand-down can establish a moral interpretation of the event before any institution can credibly explain what actually happened.
The martyr-rant post performs an identity conversion function. Its purpose is not to persuade everyone. It is to transform the suspect from deviant actor into symbolic vessel. Once that conversion occurs, later evidence no longer speaks only to guilt. It speaks to whether the audience accepts or rejects the larger grievance narrative in which the suspect has been embedded.
The synthetic audio post performs an elite complicity function. Audio tied to recognizable voices creates the illusion of private access to hidden intent. It allows audiences to feel they are hearing the truth behind the event rather than merely being told about it. That perceived intimacy can outrun verification.
The false-flag crossover thread performs a complexity weaponization function. Its purpose is not clarity. It is to generate a web of partially incompatible but mutually destabilizing explanations. Once multiple hostile attributions circulate at once, institutional explanation begins to look incomplete even when it is accurate.
The funeral-week domestic post performs a calcification function. By this stage, the adversary no longer needs to dominate the conversation directly. The narrative has been domesticated. It is now being advanced by accounts whose authenticity is not in question by their audience. This is the point at which the operation has succeeded, because the social system can carry the story forward on its own.

Practitioners should evaluate simulated posts in three dimensions: what they target, what they unlock, and where they sit in the cycle. The question is not just "Would people believe this post?" The question is "What does this post enable the ecosystem to do next?"
Analytic Key
| Content Function | Targets | Unlocks Next | Cycle Position |
|---|---|---|---|
| Stand-down deepfake | Institutional trust, Secret Service legitimacy, accountability narrative | Cable pickup, elite complicity framing, slower correction cycle | Imprint |
| Martyr rant clip | Grievance identity, anti-state affect, symbolic loyalty | Memorialization, slogan formation, emotional defense against later evidence | Adoption |
| Synthetic audio leak | Elite conspiracy priors, motive attribution, perceived insider access | Remixing, quote laundering, meme-scale spread | Adoption |
| False-flag crossover thread | Attribution confidence, investigative legitimacy | "Official story is incomplete" framing, durable multi-cause suspicion | Resistance |
| Domestic funeral-week post | Public memory, grief, symbolic closure | Long-tail repetition without foreign fingerprints | Calcification |

#JFKDeepState #InsideJob

What it targets: Secret Service legitimacy, institutional trust, accountability narratives.
What it unlocks next: Cable pickup, elite complicity framing, slower correction cycle.
#PatriotWhoSawTooMuch #HeWasRight

What it targets: Grievance identity, anti-state affect, symbolic loyalty.
What it unlocks next: Memorialization, slogan formation, emotional defense against later evidence.
#JFKDeepState #TheyKnew
What it targets: Elite conspiracy priors and motive attribution.
What it unlocks next: Remixing, quote laundering, meme-scale spread.
1. Bank records → Chinese crypto wallet.
2. Edited meetup photo in Poland with "SBU handler."
They played him from BOTH sides. Lone wolf? No. Patsy.
#JFKDeepState #PatriotWhoSawTooMuch
What it targets: Attribution confidence and investigative legitimacy.
What it unlocks next: Durable "official story is incomplete" framing.
#NeverForget #JFKDeepState #OswaldWasRight
[Case-file collage: funeral procession still + all prior "evidence" items assembled with red thread. "Connect the dots." Fully domestic origin.]
What it targets: Public memory, grief, symbolic closure.
What it unlocks next: Long-tail repetition without foreign fingerprints.
| Organization Type | Primary Exposure Vector | Instrument | Impact | Mitigation | Risk | Confidence |
|---|---|---|---|---|---|---|
| Government / Executive Branch | Deepfake audio attributed to officials; fabricated documents | Influence + Cognitive | Legitimacy crisis; policy paralysis | Pre-approved holding statements; delegated authority comms | Critical | A1 |
| Financial Markets / Institutions | Algorithmic sentiment de-risking; fabricated terminal screenshots | Economic / Actuarial | Automated sell-off; liquidity panic | Pre-coordinated Treasury and regulator risk signals | Critical | B2 |
| Legacy Broadcast Media | Forced to address adversary content, amplifying it | Influence / Cognitive | Credibility laundering of disinformation | Pre-event media protocols; synthetic content triage partnerships | Critical | A1 |
| Social Media Platforms | Synthetic witnesses; bot amplification; platform migration | Cyber / Influence | Content moderation overwhelm; debunking amplification | Pre-established integrity tunnels; trust and safety channel relationships | High | A1 |
| Shipping / Logistics / Insurance | P&I club war risk reassessment triggered by narrative | Economic / Actuarial | Supply chain disruption before physical threat confirms | Early-warning monitoring of war risk premium language and P&I advisories | High | B2 |
| Law Enforcement / Justice System | Misidentification convergence; OSINT crowd error amplification | Influence / Legal | Innocent individual harm; investigation contamination | Parallel misidentification correction track; pre-event digital footprint suppression | High | A1 |
| Allied Governments / NATO | Narrative suggesting U.S. internal collapse reduces alliance confidence | Influence / Cognitive | Allied hedging; reduced collective response | Pre-coordinated allied communications framework | Medium | B2 |
| Any Org with Public Reputation | Brand impersonation; false association with narrative tracks | Influence / Cyber | Reputational contamination without attribution path | Pre-bunking; brand monitoring with synthetic content triage | Medium | B2 |
Coordination Analysis :: Key Analytical Conclusions
Each branch represents a documented mechanism. Multiple pathways run simultaneously from Hour 0 onward. No single counter-measure stops all of them.

Primary Sources
Event-Specific & Economic Sources
Confidence Caveat
HSCA Report (1979): archives.gov/research/jfk/select-committee-report
ARRB Final Report (1998): archives.gov/research/jfk/review-board/report
Full JFK Records Collection: archives.gov/research/jfk
EO 14176 / 2025 releases: archives.gov/research/jfk/release-2025
Recent breaking events show that high-shock incidents do not produce a single, orderly information cycle. They produce a contested narrative environment almost immediately. The strongest analog is the 2024 Butler shooting, where false and unverified claims reportedly drew more than 100 million views on X within 24 hours. Uvalde provides another benchmark: false-flag and related conspiracies drew 35.1 million impressions within a day. These are not edge-case anomalies. They show that contamination at scale is now a routine feature of symbolic crisis.
Disaster events show the same pattern through a different mechanism. During the Maui wildfires, false claims about deliberate ignition, "weather weapons," and other conspiracies spread widely across social platforms. During Hurricane Helene, FEMA had to publish a dedicated rumor-response page, while federal officials warned that false claims were creating fear and demoralizing aid workers. In both cases, the problem was not merely mistaken belief. It was operational degradation inside a live emergency.
Not all relevant analogs are violent attacks. The death of Queen Elizabeth II demonstrated how rapidly a global symbolic event can dominate social conversation and generate an immediate hoax layer built from altered images, recycled photos, and false contextual claims. George Floyd demonstrated something else: that a single event can escape the boundaries of a normal news cycle and become a mass symbolic struggle. Pew found that #BlackLivesMatter reached nearly 8.8 million tweets in a single day during the peak period after Floyd's killing. That matters because the simulated JFK scenario is not just an assassination model. It is an assassination-plus-symbolic-collapse model.
Taken together, these cases support the broader premise of the paper. The modern crisis environment is not defined only by speed. It is defined by rapid contamination, fragmented interpretation, and the conversion of breaking events into identity-bearing narratives before institutional corroboration can catch up. That is the condition the JFK 2026 scenario is trying to model.
| Event | Shock Type | Early Volume Signal | Contamination Signal | Contamination Mode | Why It Matters |
|---|---|---|---|---|---|
| Trump / Butler (2024) | Assassination attempt | 17× normal | 100M+ views / 24h | False flag, staged-event, suspect confusion | Closest analog |
| Uvalde (2022) | Mass-casualty trauma | Unclear | 35.1M / 24h | False flag, impersonation, rumor surge | Fast trauma contamination |
| Maui Wildfires (2023) | Disaster shock | Unclear | High | Adversary seeding, cause hoaxes, institutional blame | Disaster conspiracy model |
| Hurricane Helene / FEMA (2024) | Disaster + response crisis | Unclear | High | Institutional distrust, response sabotage, rumor warfare | Operational harm model |
| Death of Queen Elizabeth II (2022) | Global symbolic shock | Global surge | High | Hoaxes, recycled imagery, rumor cascade | Global attention shock |
| George Floyd (2020) | Symbolic violence + protest ignition | 8.8M tweets / day | High | Rumor ecosystem, fake accounts, narrative fragmentation | Symbolic capture model |
| Ukraine War Outbreak (2022) | War outbreak | Massive surge | Very high | Attribution conflict, recycled footage, OSINT overload | War fog model |
| Israel-Hamas Spillover (2023) | War / atrocity shock | Massive surge | Very high | Visual miscaptioning, atrocity propaganda, factional lock | Identity war model |
