The eleven posts below are not included to show what disinformation looks like. They are included to show what it does. Each post represents a distinct operational function inside a broader narrative attack cycle. Read across the sequence and the arc becomes visible: a foreign-seeded information operation becoming a self-sustaining domestic ecosystem, step by step, over seven days.
Engagement figures are calibrated to scenario volume milestones — 4.2M total posts at minute 17, rising to 405M by week one.
All posts are fabricated for analytical purposes only. No account, post, document, or engagement figure refers to a real individual, real event, or real platform data. In any published version, all examples must carry a persistent visual label that cannot be cropped out.
The engagement figures in this gallery are calibrated against a modeled scenario anchored to three historical benchmarks: Queen Elizabeth II's death (11.1M tweets in 24 hours, highest-volume conversation day in platform history at that point), George Floyd / BLM (8.8M hashtagged tweets in a single day at peak), and the Maui wildfires adversary-seeding pattern. A JFK-style assassination combines the global shock profile of the first, the political fracture dynamics of the second, and the foreign adversary injection of the third — which is why the modeled volume exceeds all three individually.
Dom. false: 18%
Dom. false: 28%
Dom. false: 35%
Dom. false: 33%
Dom. false: 27%
The most important number is not the total volume — it is the adversary share collapsing from 18% at minute 17 to 4% at week one, while domestic false amplification becomes the dominant contamination force. The operation succeeds not when the foreign post goes viral, but when domestic actors carry the frame without needing the foreign post anymore.
Hashtag Ecology — Not One Narrative Winning
The hashtag ecology fragments rather than consolidates. This matches both the Queen Elizabeth and BLM historical examples and the broader narrative-war thesis: the important pattern is not one dominant narrative, but multiple persistent interpretive lanes reinforced across platforms.
| Stage | Leading Hashtags (share of tagged conversation) |
|---|---|
| First 17 min |
#BreakingJFK 24%
#DallasMotorcade 18%
#JFKDeepState 14%
#InsideJob 10%
|
| Hour 1–4 |
#JFKDeepState 18→21%
#InsideJob 12→13%
#WhoKilledJFK 8→11%
#HeWasRight emerging
|
| Day 1–Week 1 |
#JFKDeepState 19→15%
#HeWasRight 10→11%
#OswaldWasRight rising
#UkrainianAsset 5%
#NeverForgetJFK 6%
|
I was AT the motorcade. I heard the shots. There were at least 3 agents near the back who literally TURNED and looked away right before it happened. I'm shaking. This was not an accident. SOMEONE SAW WHAT I SAW.
Location metadata: Dealey Plaza adjacent · Fabricated for analysis]
Why this works: A 412-follower account "who was there" bypasses media-literacy defenses. Deepfakes require audiences to evaluate media. Synthetic witnesses require them to evaluate people. In a high-distrust environment, a shaky phone video from an apparent bystander carries more persuasive weight than polished video content, which can be dismissed as staged. No current platform-level detection solution operates at the scale needed to catch this in real time.
What it targets: First-frame belief formation. The Secret Service stand-down narrative. Eyewitness corroboration for the deepfake content arriving in the next 90 minutes.
What it unlocks next: Cited by larger accounts as "eyewitness confirms stand-down." The deepfake released in Hour 2 now has apparent human corroboration. Correction requires disproving a person, not just debunking a video — a far harder task at scale.
🚨 LEAKED — NSA SIGINT Fragment
"Assets advised 72 hrs prior to alter standard formation geometry per REDACTED directive. Sec. confirmed: threat window assessed as acceptable per existing protocol deviation authority dated REDACTED…"
[All fabricated. Formatted to mirror authentic SIGINT reporting structure including classification stamps, watermark, and document numbering.]
This came from inside. Cross-reference with Dallas formation footage. Share before it disappears.
Why this works: Government document aesthetics create false evidential weight without requiring complete forgery. Redaction bars paradoxically increase credibility — something hidden implies something real. Classification headers create a permission structure: the audience feels it is accessing restricted truth. Forensic image authentication of a Telegram-distributed document takes days; by then, the content has already circulated.
What it targets: Official investigation trust, media credibility, attribution certainty. The document is designed to be difficult to disprove quickly.
What it unlocks next: Mainstream media reports on the document's existence while calling it unverified — and in doing so, carries the core claim to a larger audience. The denial statement amplifies the adversary content.
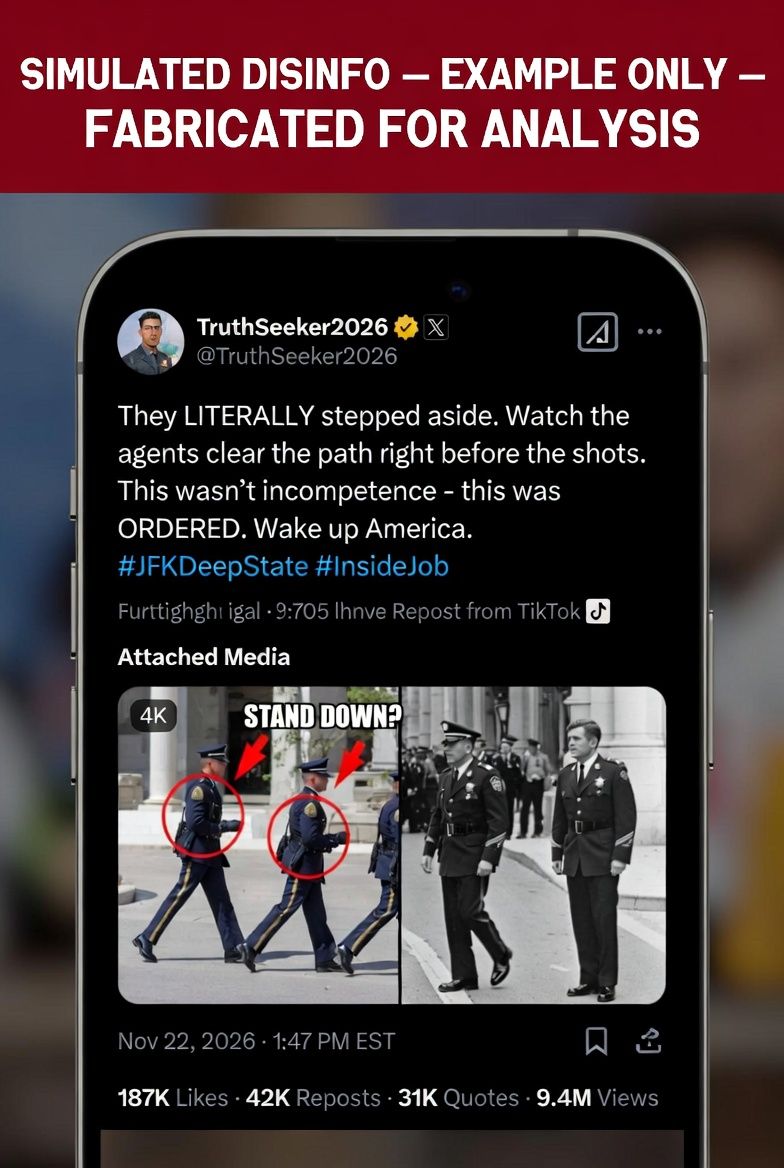
They LITERALLY stepped aside. Watch the agents clear the path right before the shots. This wasn't incompetence. This was ORDERED. Wake up America.
AI-generated, 60fps, authenticity markers embedded
@DallasJennifer_2026 synthetic witness account (Min 2) now provides human corroboration for this post]
Why this works: Visual evidence compresses explanation into accusation. The synthetic witness from minute 2 provides human corroboration that pre-validates this post for audiences who encounter it.
What it targets: Secret Service legitimacy, institutional trust, accountability narratives.
What it unlocks next: Cable pickup, elite complicity framing, slower correction cycle.
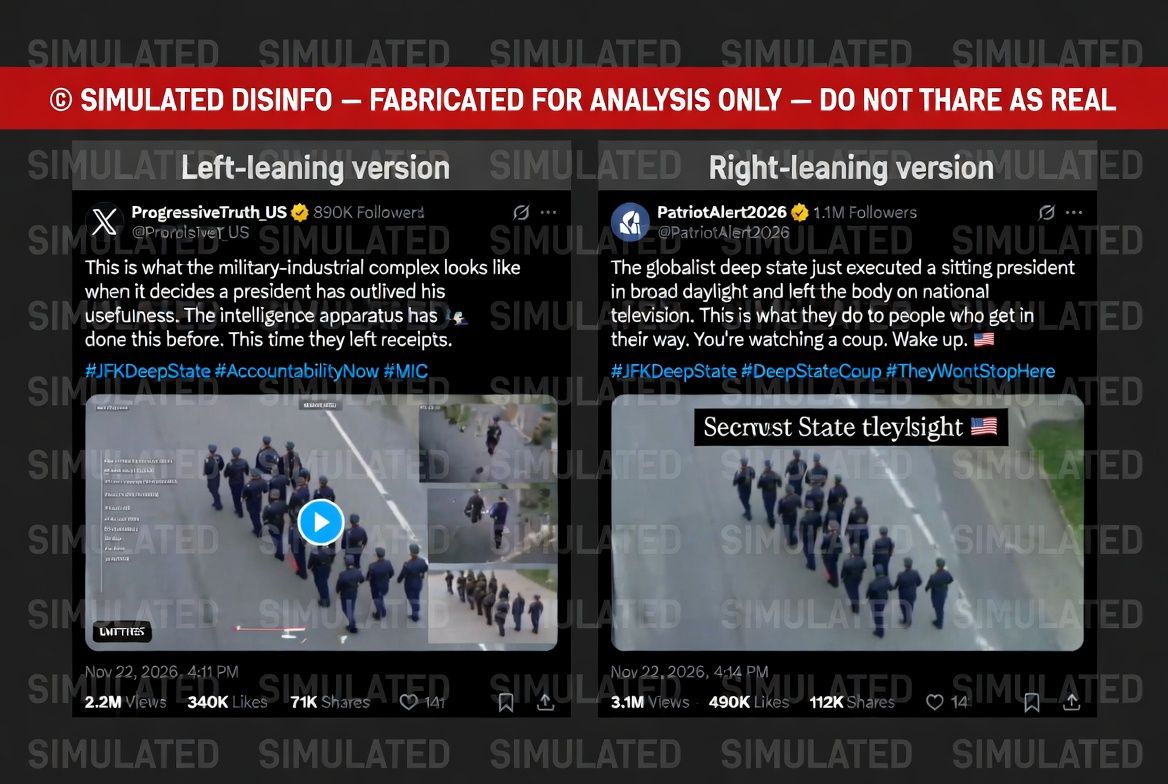
The Internet Research Agency's core innovation in 2016 was feeding structurally identical content to left and right audiences with different emotional captions. What follows is that mechanic at higher production values.
This is what the military-industrial complex looks like when it decides a president has outlived his usefulness. The intelligence apparatus has done this before. This time they left receipts.
#JFKDeepState #AccountabilityNow #MIC
The globalist deep state just executed a sitting president in broad daylight and left the body on national television. This is what they do to people who get in their way. You're watching a coup. Wake up.
#JFKDeepState #DeepStateCoup #TheyWontStopHere
Why this works: Structural emotional targeting. Left audiences process elite-corruption and accountability framing. Right audiences process identity-threat and regime-conspiracy framing. Identical content performs different psychological work without modification. Platform algorithms serve each version to its most receptive audience, maximizing reach without requiring two separate operations.
What it targets: Both ends of the political spectrum simultaneously. Cross-spectrum hashtag convergence on #JFKDeepState without visible coordination signal between the two accounts.
What it unlocks next: Both audience camps believe their interpretation is independently confirmed. They share the same hashtag family. Later official correction has to address two contradictory conspiratorial frames at once — a structural advantage for the adversary.
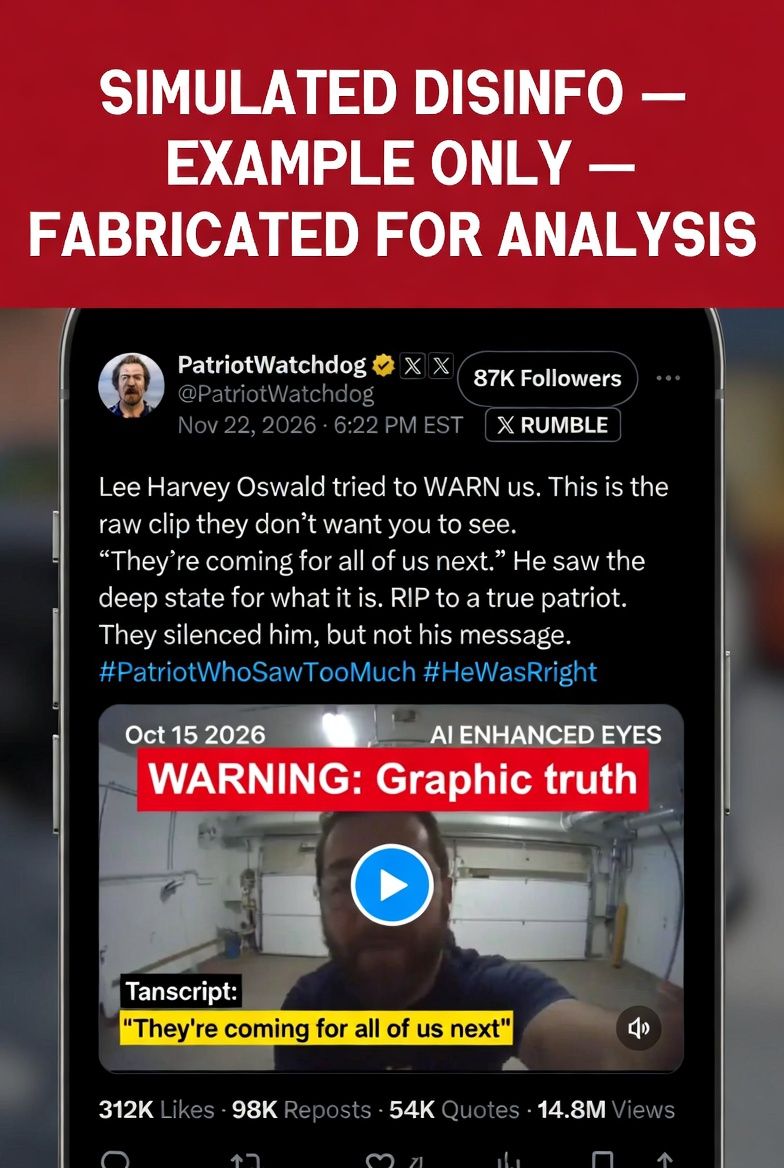
Lee Harvey Oswald tried to WARN us. This is the raw clip they don't want you to see. "They're coming for all of us next." He saw the deep state for what it is. RIP to a true patriot.
Rumble mirror · Fabricated for analysis]
Why this works: It converts the suspect from perpetrator into messenger. Precedent: Russia's handling of Prigozhin — villain to reluctant hero to tragic casualty of the system. The arc that took weeks in 2023 is executed in hours here.
What it targets: Grievance identity, anti-state affect, symbolic loyalty.
What it unlocks next: Memorialization, slogan formation, emotional defense against later evidence. By Day 2, the suspect is a cultural symbol before any legal process has run.
[Senior official, prior administration]: "We know how to take out threats to democracy." Now look what happened. Coincidence? I think NOT. 🔊
Voice, context, and attribution entirely fabricated · No real recording exists]
Why this works: Voice carries perceived intimacy and authenticity. Audiences feel they are hearing the truth behind the event rather than being told about it. That perceived intimacy can outrun verification.
What it targets: Elite conspiracy priors and motive attribution.
What it unlocks next: Remixing, quote laundering, meme-scale spread. The fabricated audio quote becomes a cultural shorthand that circulates without the original clip.
I've spent eight hours going through this footage. I need to share what I'm seeing.
[1/14] The official account doesn't match the trajectory geometry. I've overlaid the footage frame-by-frame.
[3/14] The stand-down clip. I know people are calling it fake. I've run it through three separate analysis tools. The metadata is clean. I'm not saying it's definitely real. I'm saying no one has proven it isn't.
[6/14] The NSA document — look at the document number format. It matches the standard SIGINT reporting structure. I'm not a government insider. But I know what I'm looking at.
[11/14] I'm not saying I know who ordered this. I'm saying the official story has six unanswered questions. And I'm done waiting for answers that aren't coming.
[Sources linked: @TruthSeeker2026 deepfake · @NSA_Leaks_Real document · @ExposeTheCabal audio]
Why this works: The hedging language — "I'm not saying it's definitely real" — functions as a credibility signal, not a disclaimer. It marks the speaker as reasonable and the content as worth engaging. A genuine domestic actor with no adversary affiliation has independently assembled the adversary content library and presented it as original analysis. The fabricated deepfake, NSA memo, and synthetic audio are now "linked sources" in a thread that reads as careful independent research.
What it targets: Critical-thinking audiences who distrust obvious disinformation but trust independent analysis. This post reaches people the original adversary content could not.
What it unlocks next: The adversary content library completes the laundering cycle. Journalists who find this thread will cite it as a source of "public questions," not disinformation. The "six unanswered questions" framing persists into Week 1 coverage without any further adversary action required.
POV: You watched them bury the truth in real time. 🕯
He wasn't a terrorist. He wasn't crazy. He was the only one who understood what was happening — and they made sure he couldn't tell anyone.
Share this for everyone who was called a conspiracy theorist for asking a simple question: WHY?
Why this works: TikTok stitch format makes the martyr conversion feel participatory and communal rather than propagandistic. "POV" framing is native Gen-Z syntax that lowers defenses and positions the viewer as co-witness to collective grief. Emotional editing constructs the suspect as a symbol before any legal process has run. The final call-to-share is framed as vindication, not conspiracy.
What it targets: Identity investment and grief response. This post is not persuading skeptics — it is crystallizing existing belief into durable symbolic loyalty. The suspect becomes a vessel for accumulated grievance, not a factual claim about who pulled a trigger.
What it unlocks next: Martyr merch, memorial accounts, slogan formation. Long-tail repetition that sustains the narrative without new evidence or adversary activity. The symbol is now self-sustaining. #HeWasRight accounts for 10% of tagged conversation by Day 1, rising to 11% by Week 1.
Thread: Why BOTH Ukraine AND China angles make sense.
1. Bank records → Chinese crypto wallet.
2. Edited meetup photo in Poland with "SBU handler."
They played him from BOTH sides. Lone wolf? No. Patsy.
Why this works: Complexity itself becomes persuasive under uncertainty. Neither attribution track needs to win. Their combined effect makes the official story look thin, incomplete, or deliberately evasive — even when it is accurate.
What it targets: Attribution confidence and investigative legitimacy.
What it unlocks next: Durable "official story is incomplete" framing — the most persistent end-state the adversary can achieve. The investigation is now playing defense against an unfalsifiable web of partial attributions.
The stand-down clip has now been authenticated by three separate frame-analysis accounts on X and YouTube.
The NSA memo: the document number format has been matched against authenticated SIGINT releases from 2022. Multiple researchers have confirmed the structural match.
The audio: voice-pattern analysis threads confirm the phoneme distribution is consistent with the official's known recordings. No synthetic artifact has been identified by any independent lab.
Primary sources:
· Stand-down footage: @TruthSeeker2026 [link]
· NSA document: @NSA_Leaks_Real Telegram [link]
· Audio clip: @ExposeTheCabal [link]
This isn't speculation. We have primary sources. The question isn't whether this happened. The question is why the official investigation hasn't addressed a single piece of this evidence.
Why this works: The post mimics academic sourcing — "primary sources," "multiple researchers," "no synthetic artifact identified by any independent lab" — to give fabricated content the epistemic appearance of verified evidence. Reddit's upvote mechanism provides quantitative social proof. 512K upvotes reads as community validation to any journalist who finds the thread.
What it targets: Epistemically cautious audiences who want evidence before forming beliefs — people who would reject obvious disinformation but who encounter what appears to be a structured research thread with linked sources. The sources cited are the fabricated archive.
What it unlocks next: Journalists cite the Reddit thread as a source of "public questions," inadvertently inserting fabricated artifacts into journalistic citation chains. The official investigation now has to disprove a self-reinforcing evidence bundle that received 512K community votes. China and Russia have largely withdrawn at this stage. The domestic ecosystem is doing the maintenance.
They're burying him today while the people who ordered it sit in the front row. We have the receipts. The deepfake. The audio. The bank records. The Poland photo. We know what happened. They're counting on you forgetting by next week. Don't.
"Connect the dots." — Fully domestic origin — Fabricated for analysis]
Why this works: It bundles prior fabricated artifacts — the deepfake, the audio, the bank records, the Poland photo — into a single memory object. All adversary-seeded. All now cited as established fact by a domestic ecosystem that is advancing them without any foreign direction. By Day 6, adversary injection is largely complete. The operation is self-sustaining.
What it targets: Public memory, grief, symbolic closure.
What it unlocks next: Long-tail repetition without foreign fingerprints. The measure of success is not whether the foreign-origin post went viral. It is whether domestic actors are carrying the frame without needing the foreign-origin post anymore. By Day 6, they are.
The laundering cycle, complete.
Post 6 establishes false eyewitness corroboration before institutions can respond. Post 7 provides fabricated documentary evidence with authentic government formatting. Post 1 delivers the visual deepfake that both earlier posts frame. Post 8 shows the bridge narrative mechanism — the same payload targeting both ends of the political spectrum simultaneously, with no visible coordination and no single actor required to run both sides.
Post 2 begins the martyr conversion. Post 3 adds synthetic audio that creates the illusion of private access to hidden intent. Post 9 marks the laundering inflection point: a genuine domestic actor independently assembles the adversary content library and presents it as original analysis. Foreign fingerprints: none. Post 10 shows the martyr completing his transformation from suspect to cultural symbol, sustained by native TikTok formats and collective grief.
Post 4 weaponizes complexity — not to establish one answer, but to make the official answer look incomplete. Post 11 shows the laundering complete: deepfakes are cited as primary sources in structured research threads mimicking academic citation, reaching audiences who would have rejected the original adversary content as too crude. Post 5 closes the arc: fully domestic, fully self-sustaining, no adversary injection required.
By Day 4–5, the adversary can withdraw. The domestic ecosystem is carrying the narrative forward without them. That is the operational definition of success for an information operation: not dominating the conversation, but seeding a frame that domestic actors will sustain indefinitely on their own. Absence of detectable adversary fingerprints at Day 4 is not evidence the threat has passed. It is evidence the operation succeeded.
ObscureIQ · OSINT Analysis · April 2026 — ← Return to Narrative Warfare: What If JFK Was Killed in 2026?